Who needs a calendar? I can always tell it’s tax season when I start getting malware-laden emails from the “IRS” in my spam folder. These typically aren’t sophisticated attackers, they are preying on how intentionally confusing and anti-consumer taxes are in the US, but mostly rely on targeting folks who aren’t aware of these scams or can’t reliably identify government websites. The quality of the emails sent often reflect that, and are ex. mass-mailed from compromised hosts which are quickly detected and blocked by major email providers.
A surprise this year was one of those emails wasn’t flagged as spam by my email provider, and went to my inbox. Disappointing! Let’s take a look at why (hint: it wasn’t due to quality) and take down this attacker’s infrastructure.
The Email
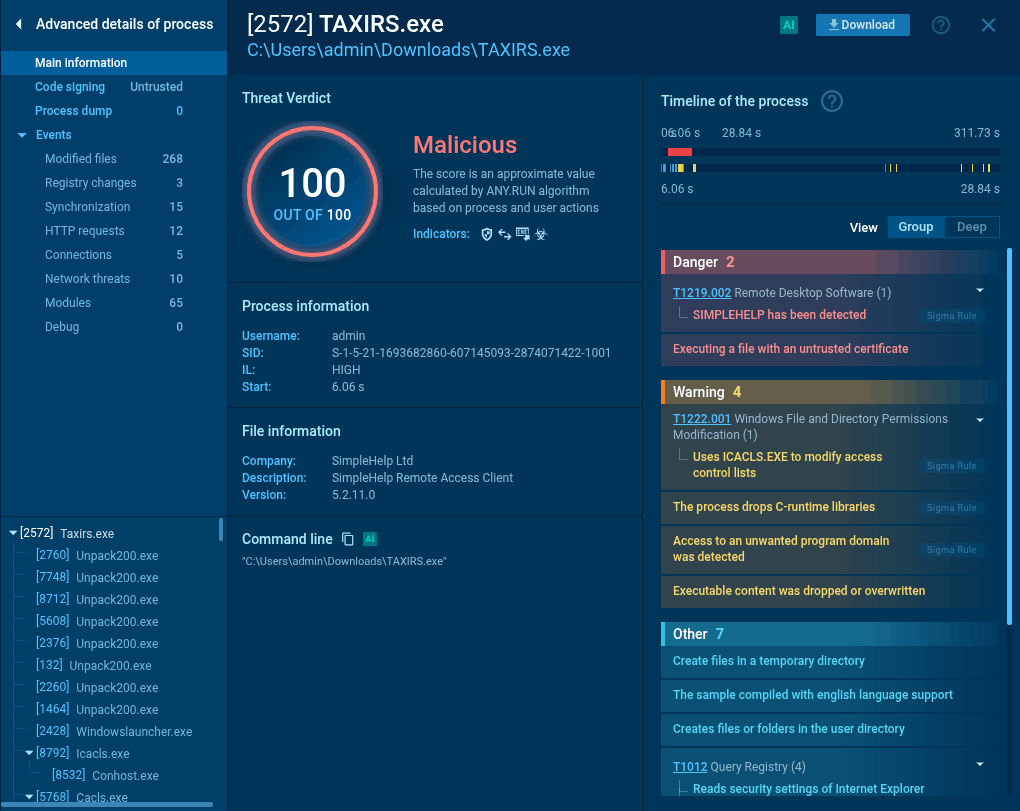
The email itself, titled “IR-2026-216” - was sent from “IRS US” via noreply@campaign.eventbrite.com. You can see this incredibly legitimate (sarcasm) IRS notification about cryptocurrency tax forms below:
A major contributing reason this email reached my inbox is because it was legitimately sent via Eventbrite - either the attacker registered or compromised an account. Per the headers below, we can see that the email from Eventbrite was signed and successfully authenticated by email provider:
Authentication-Results: mail.protonmail.ch; dkim=pass (Good 1024 bit
rsa-sha256 signature) header.d=campaign.eventbrite.com
header.i=@campaign.eventbrite.com header.a=rsa-sha256
Authentication-Results: mail.protonmail.ch; dmarc=pass (p=reject dis=none)
header.from=campaign.eventbrite.com
Authentication-Results: mail.protonmail.ch; spf=pass smtp.mailfrom=bounce.eventbrite.com
Authentication-Results: mail.protonmail.ch; arc=none smtp.remote-ip=156.70.3.100
Authentication-Results: mail.protonmail.ch; dkim=pass (1024-bit key)
header.d=campaign.eventbrite.com header.i=@campaign.eventbrite.com header.b="gXWPpCEp"
And as Eventbrite is often used for legitimate, mass-email purposes, they are less likely to be flagged by email providers automatically as spam. However, this seems to be one of relatively few smart choices the attacker has made for their campaign.
Looking more closely at the email itself, the lure is very vague, stating only that I need to view a document “on a computer only” within 72 hours related to cryptocurrency transactions filed in 2025. The email is not well-formatted and not compelling, but most interestingly, the link to the website where we’ll be served malwa– erm, documents, is not even a link - just the text ..gov-irs216.net/IRS/.
Perhaps this is a mistake rather than intentional, but the lack of a hyperlink likely also contributes to why the email wasn’t flagged as spam, because there isn’t actually any link to an unknown site which would be recognized by anti-spam tools. Unlike using Eventbrite (which was smart), the lack of a hyperlink seems to be very dumb. Any human target who receives this email is going to 1. need to copy and paste the URL into their browser, and 2. that URL is going to be scrutinized more while the target copies and pastes it into their browser.
In either case, let’s pretend we’re fooled and visit the gov-irs216.net website.
The “IRS” Website
After pasting the URL into our browser, we are presented with the following comic relief:
With highlights including:
- The URL,
https://gov-irs216.net/IRS/TAXIRS2026-CRYTPO.phpis super convincing and doesn’t even spell “crypto” correctly. - After the timer hits zero, the target is sent to
https://gov-irs216.net/IRS/TAXIRS.exe, initiating the malware cough erm, document download. The file isn’t - at all - attempting to present itself as a document, but we’ll get to that. - There is absolutely no call to action on this page, no further redirect, or encouragement for the target to open the file being downloaded. The timer just reaches zero and the site sits there, stating “⏳️ establishing secure connection” and “0 seconds.”
- Despite there being no actual effort to impersonate Cloudflare, the title is
Cloudflare style · loading. Apparently Cloudflare has a monopoly on interstitial loading screens with orange highlights. - “✅ encrypted” at the bottom of the page. Hell yeah. Super secure.
The attacker is clearly working on this live. In the past 24 hours, they updated the URL of the fake interstitial page (it was previously even-less-convincing: https://gov-irs216.net/IRS/ss.php) and updated the URL where the file is being served (it was previously titled: Taxid.exe).
Poking around, the site itself is hosted by CloudAccess.net, a legitimate, managed Joomla/Wordpress hosting provider. The site itself is running WordPress, and the administrator account is a seemingly keyboard-smashed username: odldrkgr. The site doesn’t appear to be compromised (e.g. it looks like the attacker created the account themselves, and the only post is “Hello world!” which is created when installing Wordpress) and has been online since February 27th, shortly before I received the email from Eventbrite.
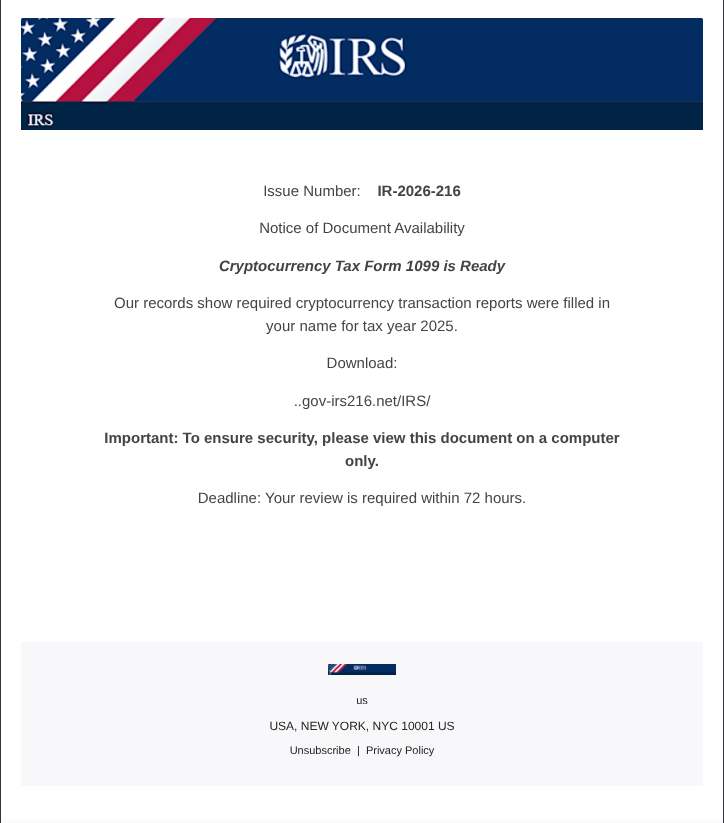
The Malware
The file downloaded is SimpleHelp, a legitimate remote management (RMM) tool which the attacker is abusing. The file makes no attempt to disguise itself as a document and is clearly an application, and it even uses the original SimpleHelp icon. Recently, there has been a lot of press around how SimpleHelp was being exploited by threat actors such as ransomware gangs, but in this case our attacker simply has a (cracked?) SimpleHelp installer and server which they’re using maliciously.
Because there are legitimate usecases for SimpleHelp, it’s less likely to be detected and stopped by antimalware on the host computer. As an example of this, as of writing only 5/72 vendors on VirusTotal consider this file malicious (though several Snort/ET rules flag its traffic as potentially unwanted).
If the victim opens the SimpleHelp installer, it quietly downloads additional version files and JRE components from http://216.126.225.94 (the attacker’s SimpleHelp server), an IP address belonging to legitimate VPS provider Cloudzy. The SimpleHelp RMM service is then launched in the background from C:\ProgramData\JWrapper-Remote Access\JWrapper-Windows64JRE-00063527423-complete\bin\Remote Access.exe - registering the computer with the same IP address, and then lying in wait for the attacker to connect and take additional actions (PCAP).
I was not able to observe the attacker connecting or deploying additional payloads, but given the cryptocurrency theme of the email it’d be pretty safe to assume the attacker is primarily after cryptocurrency - and they would be likely looking to remotely log in to the victim’s computer, access their wallets or exchanges, and then empty them. Exchanges in particular would be a great target, as the victim’s computer would likely already be logged in to email and messaging services that exchanges would use for 2FA (if the victim is not using higher security options such as TOTP or hardware keys).
Conclusion
In summary, using a legitimate RMM tool to access computers and (likely) trying to steal cryptocurrency is a surprisingly smart final stage which could allow the attacker to silently compromise and maintain access to victims’ computers - especially after many clear signals throughout the experience that this is not a legitimate message from the IRS. I expect with further refinement, this could become much more convincing and start to fool people.
Unfortunately for the attacker, I will burn the infrastructure mentioned and will be filing abuse reports to the relevant hosts, and I will be following up to ensure the attacker’s C2 server especially is taken offline so they lose access to any victims (hopefully none) they’ve amassed so far.
Stay safe, and to all my fellow United States citizens, please enjoy filing your yearly taxes and paying the tax preparers that take billions of dollars from us while lobbying against making taxes free or easy to file.